Finding cyber talent is challenging enough, but the public sector’s national security and social services concerns make the hunt even harder.
In this Cybersecurity Minute, Chris analyzes how the digital infrastructure of Costa Rica is falling prey to cyber crime.
Although there are differences between the private and public sectors, there is also more overlap than we hear from social media conjecture.
From supply chain software to workforce changes, future cybersecurity trends require closer looks by companies looking to make their systems more resilient.
While zero-day vulnerability attacks still occur, new research emphasizes the need for basic security hygiene to protect against most advanced persistent threats.
Chris addresses reports that more than 80% of Kubernetes API servers are exposed to the public internet.
As more companies embrace a decentralized workforce, they must increase cybersecurity efforts for remote work environments.
Cloud-based systems all have their own risks, which makes security particularly critical for SMBs in order to keep their data safe.
Kubernetes opens up an attractive opportunity to do multi-cloud deployments in a way that doesn’t conjure up nightmares. Here are a few things to consider.
Chris addresses FBI, CISA, and NSA warnings that managed service providers that are also SMBs are increasingly popular targets for supply chain attacks.
As technological systems become more complex through Cloud, microservices, IoT, and more, the need for sound vulnerability management is even more paramount.
We explore the reasons for its infamous rise. Regardless, organizations need to increase efforts to secure app access.
In this Cybersecurity Minute, Aaron looks at Oracle Cloud’s new security features and the use of machine learning in cloud data threat assessment.
Okera’s Bobby Napiltonia and Nong Li join Acceleration Economy analysts Wayne Sadin and Aaron Back to discuss data stewardship in a time of expanding regulations and compliance requirements.
As supply chain complexity has exploded, CISOs need to map out the risk management strategies for their organizations.
From military submarines to astronomers charting the night sky, remote access is everywhere & poses a serious threat if left without security.
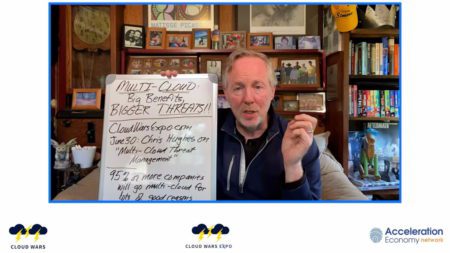
At Cloud Wars Expo, cybersecurity specialist and analyst Chris Hughes will speak on multi-cloud threat management.
In this Cybersecurity Minute, Chris talks about efforts being made to improve open-source software security by OpenSSF.
While secrets management has been a challenge, it’s critical that organizations have a game plan for when a credential leak occurs.
Shortly on the heels of the Log4j is a new exploit in the Spring Framework, Spring4Shell. Here we explore what it is and how to mitigate it.