In life, as in business, it’s not just about who you depend on that matters — it’s who they depend on as well. And just as in human relationships, software ecosystems comprise a vast network of relationships. Some of these ties go very deep, while others are more surface-level. But the fact remains: Modern open-source-based software (OSS) development involves a vast dependency tree with long roots that touch known and unknown risks.
A recent Endor Labs report found that 95% of vulnerable dependencies are transitive ones. These transitive dependencies are components tucked deep into the software chain, making them more challenging to assess and reach. And it’s not necessarily that these vulnerable packages are far outdated — 25% of packages released in 2022 still have between one and 18 known vulnerabilities.
New vulnerabilities around open-source dependencies continue to present themselves on a daily basis. Recent software supply chain chaos adds another layer to the maintenance burdens of “dependency hell.” And although non-profit organizations and government bodies have sought to improve open-source security and introduce regulations around securing third-party software, the industry is still a long way off from having the standards and techniques necessary to stem the tide.
Endor’s 2022 State of Dependency Management study looks at the intricacies of modern open-source-based development and offers guidance. Below, I’ll summarize the study’s main points to better understand the state of dependency management and how cybersecurity professionals should respond.
Understanding Transitive Dependencies
A direct dependency is when an app directly relies on a certain library or package to function. A transitive dependency, on the other hand, is a dependency embedded within a package. As one can imagine, there could be multiple levels of transitive dependencies that app developers unknowingly insert into their applications by including other dependencies. Chart 8 from the report visually depicts how transitive dependencies come to live within downstream applications:
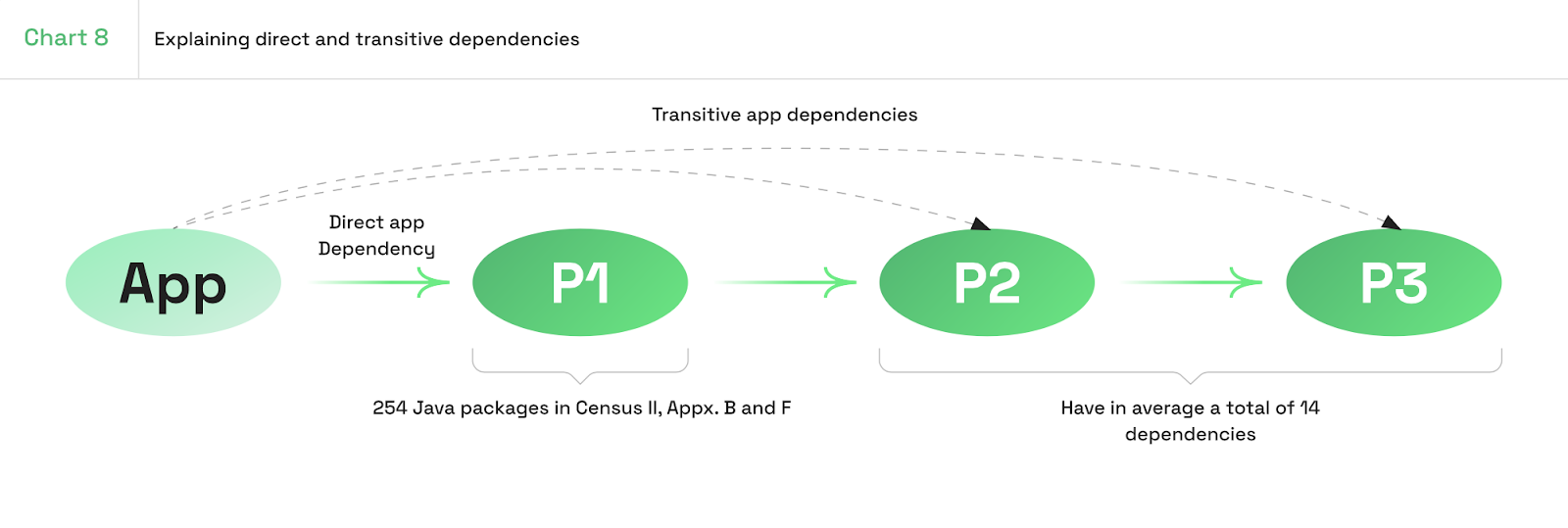
The report found that the average depth is two steps away, but it could get as far as seven in some cases.
For this study, Endor Labs took a data set from the Census II report, which provided a list of the most popular free open-source software (FOSS), and enriched it with other sources. The data, open-sourced on GitHub, represents a scan of production applications covering popular distributions such as npm, maven, nugget, pipit, and ruby gems.
Out of the 254 distinct Maven packages mentioned in the Census II dataset, most have an average of 14 dependencies. This might not seem very high, but given that most applications have dozens, if not hundreds, of dependencies, the likelihood of an application possessing affected transitive dependencies rises exponentially.
As such, there’s a 32% chance a random Maven package will have one or more known vulnerabilities hidden in its dependency tree. Some outliers have far more dependencies, increasing the chances of potential vulnerabilities. For example, log4j-core v2.19.0 had 141 dependencies, and aws-java-sdk v1.12.316 was found to have a staggering 331 dependencies.
Solutions and Tips to Manage Dependencies
In a cloud service provider (CSP) world, security responsibility is shared. The CSP secures the infrastructure, and the consumer secures the apps and media built on top of it. However, in the open-source world, the security burden largely falls into the hands of the software consumer.
“OSS consumers keep overall responsibility and need to address security risks according to their specific circumstances.”
That being said, we have seen substantial movement from regulatory bodies to establish more standards concerning third-party dependencies. These include the Candidate EU Cybersecurity Certification Scheme for Cloud Services, White House Executive Order 14028, and guidelines from NIST, NITIA, and ENISA.
Furthermore, non-profit groups like OpenSSF, CNCF, and OWASP continue to disseminate best practices and develop relevant security tooling. Yet, software providers must still take it upon themselves to ensure that their dependency trees are stable and free from major vulnerabilities.
Here are some tips, culled from the report, on how to respond:
Contribute to open-source projects. As I’ve previously covered, too many companies use open source without contributing back to the projects. Open source requires a group effort to improve, but in proportion to their high usage rates, few organizations actually support them and report security exploits.
Build a smarter culture around software acquisition and dependency management. Software providers need to dive deeper into “dependency hell” to audit their surface area and discover what they rely on. This also means updating old components in the dependency tree and being more selective during acquisition to avoid malicious packages.
Remove unused dependencies. If a program does not invoke a dependency in an upstream project, it is best to remove it. This can reduce the probability of hidden vulnerabilities and also minimize bloat. As the report says, software composition analysis (SCA) tools should prioritize analyzing dependencies that will actually show themselves in production, not ones solely used for testing purposes.
Prioritize high-risk and reachable vulnerabilities. You’ll likely want to quickly fix exploits with high CVSS scores. Yet, also consider the reachability of the vulnerability since hackers might target low-risk ones simply if they’re easier to exploit.
Time your updates right. The study found that only 9% of updates require a major version change. Yet, 20.1% of non-major releases cause breaking change! Dependency updates can take time and effort to debug, yet leaving them unaddressed can leave major exploits prone to attack. So, it’s good to set up a regular update cadence that works for your team.
Software Ages Like Milk, Not Wine
In recent years, we’ve witnessed big exploits such as SolarWinds, Log4j, and Spring4Shell, and this year the Apache Commons Text Vulnerability and protestware came into focus. Typo-squatting and dependency confusion attacks will also likely continue in the year to come, along with unforeseen attack vectors.
And with all we know now, responding to these risks will require ongoing vigilance. Because unfortunately, if left to sit, software is quick to rot. “Software is like milk — it gets sour quick,” as one line in the report puts it. Knowing how interconnected the modern dependency tree is, it’s essential to maintain oversight of the growing number of dependencies — and their vulnerabilities — that make up modern software ecosystems.
Want more cybersecurity insights? Visit the Cybersecurity channel: