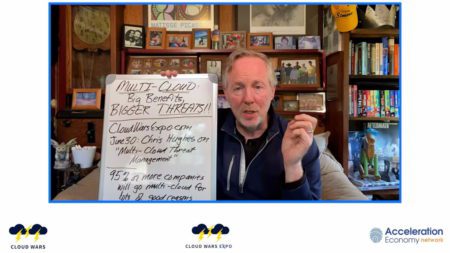
At Cloud Wars Expo, cybersecurity specialist and analyst Chris Hughes will speak on multi-cloud threat management.
Cybersecurity
In this Cybersecurity Minute, Chris talks about efforts being made to improve open-source software security by OpenSSF.
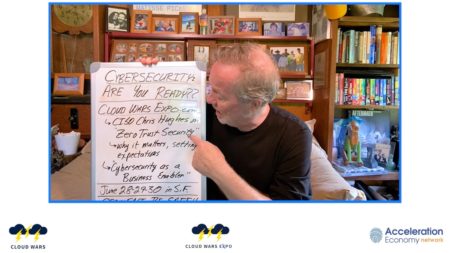
At Cloud Wars Expo, CISO and analyst, Chris Hughes will be taking the lead on cybersecurity, with one major theme being zero trust security.
While secrets management has been a challenge, it’s critical that organizations have a game plan for when a credential leak occurs.
Shortly on the heels of the Log4j is a new exploit in the Spring Framework, Spring4Shell. Here we explore what it is and how to mitigate it.
Although some may think that robots are going to replace humans, there are many beneficial aspects of using AI as an assistant.
In this Cybersecurity Minute, Chris talks about NIST’s updated C-SCRM Guidance based on tasking from the Cyber Executive Order from the President.
As containers are changing the tech landscape, business leaders need to understand containerized applications, orchestration, and security.
In today’s digitally-driven world, fostering cyber resilience in global, digital ecosystems is critical to ensure secure innovation.
AI can bridge a gap for small businesses and have a major impact when integrated in these four prime areas.
In this Back @ IT episode, Aaron hosts a conversation with Robert Wood to discuss how a cybersecurity framework can add value.
The backdrop of big data has changed the relationship between the IT department and Business Analysts across data, cloud, and cybersecurity.
As there is much excitement about the emerging virtual world, many still can’t help but question the level of security in the Metaverse.
Multi-cloud services are often associated with their own identities, permissions, authentication, and authorization activities.
In this Cybersecurity Minute, Chris discusses action being taken by the SEC to ensure cybersecurity expertise at the board level.
Data from Cloudflare exposes the top threats facing today’s web applications, including HTTP malformed requests, insecure API, & bots.
In this Cybersecurity Minute, Chris reports an advisory from federal agencies warning about nation-state hackers.
Security monitoring is one part of an overall effective security strategy. What tools will compliment your organizations strategy?
Identity has become the new perimeter in modern Zero Trust aligned environments. So, what are the fundamentals of digital identity security?
Organizations that invest in data privacy encounter a major opportunity to build trust with their customer bases and partners.