Executives from Lookout and Pax8 discuss their new partnership to enhance mobile security for small and medium-sized businesses through a cloud marketplace.
breach
Wiz’s AI Security Posture Management (AI-SPM) addresses security and privacy concerns wrought by AI with comprehensive oversight, inventory management, and misconfiguration checks.
GitGuardian’s unique Honeytoken capability proactively detects and mitigates software supply chain attacks.
Snyk shifts security left with its Deep Code AI Fix, a proprietary AI engine that automates security fixes for developers, enabling risk reduction and addressing vulnerabilities in cybersecurity.
GitGuardian and Snyk join forces to strengthen cloud-native security, enhance their developer-centric approach, and drive early risk mitigation in software development.
Cyber attacks pose financial and reputational risks, which necessitate investment in strong endpoint security defenses.
There are unique endpoint security challenges associated with cloud-based systems. Here are some strategies to address them.
Try framing cloud security conversations in terms of business outcomes and using analogies for better results.
Organizations need to invest in the right people, processes, and technologies to protect themselves from online threats in particular.
Cybersecurity data can empower C-suite executives to make informed decisions, protect their organization, and drive business growth.
Multi-cloud incident response is more complex than traditional incident response. Frank Domizio explains how and why organizations need to adapt.
Environmental, social, and governance frameworks are on the rise, and they must be crafted with enough security considerations to ward off increased cyber threats.
To prevent data breaches, organizations must prioritize data governance; there’s a big collaboration opportunity between the CISO and CDO roles in this endeavor.
The zero trust security framework can protect sensitive data from evolving cyber threats, says Frank Domizio.
These six cybersecurity practices can help board members create robust protocols to protect their organizations against diverse threats and attacks.
Multi-cloud provides flexibility, scalability, and cost efficiency, but securing this architecture requires a comprehensive approach. Frank Domizio explains.
Data security strategy must go beyond securing a company’s data and employees to protect every data channel and counterparty. Wayne Sadin presents guidelines for managing third-party data risks.
Knowing the types of data that cybercriminals target for identity theft, financial fraud, or other malicious activities helps security teams implement effective protection.
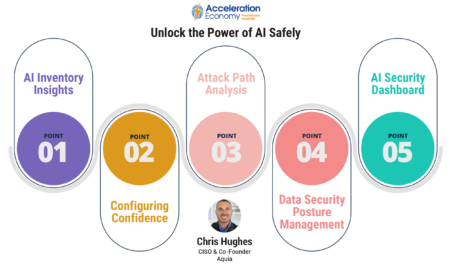
Nearly all cloud security incidents are due to customer misconfigurations. Chris Hughes explains how cybersecurity hygiene addresses the problem.
Frank Domizio explains how AI is becoming increasingly popular within the realm of cybersecurity, noting the applications of this technology.