Google Cloud’s latest quarterly results reveal its accelerating growth, impact of its partnership with Oracle, and major advancements in AI and cybersecurity.
Snowflake delivers mandatory multi-factor authentication (MFA) option so customers can exert stronger access controls.
The Crowdstrike/Microsoft outage demonstrates interdependencies in the software supply chain that can impact customers in the event of an problem with one service.
A massive software outage impacting Microsoft customers underscores the need for IT resiliency, resources that can respond quickly when systems go down.
Microsoft, IBM Consulting extend partnership with cybersecurity services that provide threat monitoring and identity management in hybrid clouds.
This guidebook offers insights from CISO Chris Hughes and CIO Kenny Mullican on maximizing multicloud benefits while mitigating its downsides.
Google’s Project Naptime utilizes AI to enhance vulnerability discovery and management, offering promising advancements in cybersecurity.
Breakthroughs in quantum computing from three Cloud Wars Top 10 firms, plus Honeywell, are opening up new frontiers in technology and industry applications.
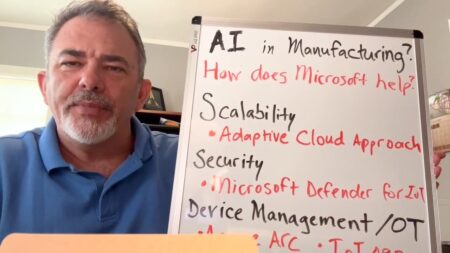
Microsoft Azure services are transforming manufacturing through AI integration, enhanced cybersecurity, and streamlined operations.
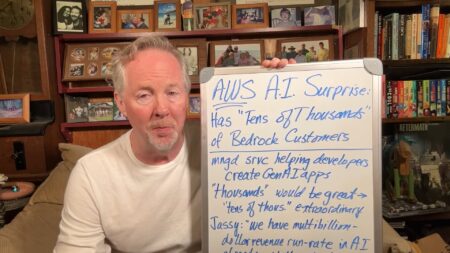
AWS’s growth in the cloud computing market includes success with its AI service Bedrock, boasting tens of thousands of customers, and demonstrates its competitive edge against Microsoft with a strong security focus.
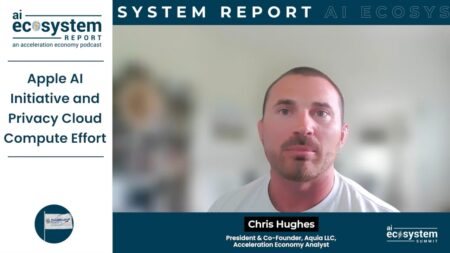
In a move to integrate AI into its products, Apple launched “Apple Intelligence” and “Privacy Cloud Compute” for enhanced privacy, with a beta release set for this fall.
Apple’s AI initiative, Apple Intelligence, will integrate AI into their devices via a partnership with OpenAI, emphasizing strong privacy measures like end-to-end encryption and Privacy Cloud Compute or PCC.
This report analyzes Microsoft’s security culture and promises of reform from CEO Satya Nadella following a widely reported breach, while highlighting the dual-edged quality of AI in cybersecurity.
The OWASP AI Cybersecurity & Governance Checklist outlines actionable recommendations for optimizing cybersecurity posture in the era of GenAI and LLM.
Executives from Lookout and Pax8 discuss their new partnership to enhance mobile security for small and medium-sized businesses through a cloud marketplace.
Partner integrates Data Security Posture Management (DSPM) with ServiceNow’s Security Posture Control tool for a 360-degree view of a customer’s attack surface.
Google Cloud’s public criticism underscores Microsoft’s cybersecurity shortcomings, as detailed in a Cyber Safety Review Board report, prompting Microsoft’s efforts to address these issues.
Aviatrix is a multi-cloud security company offering a centralized control plane to manage configurations, networking, and security across various cloud service providers.
HYCU and Dell expand their respective ecosystems around data protection technology by extending their integration efforts to new platforms.
Analyzing Microsoft’s recent cybersecurity challenges, including deficiencies in its security culture, the introduction of the Secure Future Initiative, and efforts to prioritize security in light of growing scrutiny and the need to regain customer trust.