Establishing a strong working relationship between the CISO and the CIO is crucial for the overall success and security of a company, writes Kenny Mullican.
Search Results: cybersecurity (1380)
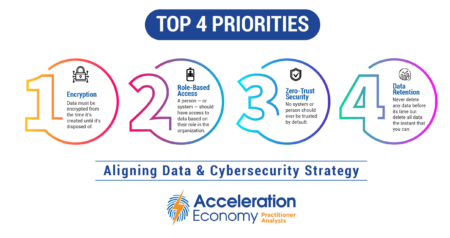
The chief data officer (CDO) and chief information security officer (CISO) should agree on encryption, role-based access, zero trust security, and data retention for effective business decisions and risk mitigation.
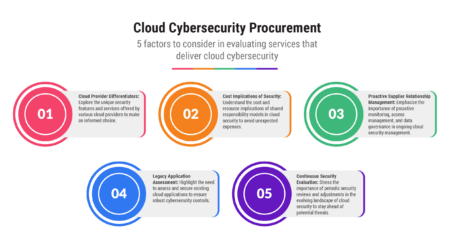
At first glance, cybersecurity models among cloud providers may seem like near carbon copies of each other, but a bit of digging can yield some real differences.
A multi-billion-dollar infrastructure investment by Microsoft in Australia will drive AI, cloud, and cybersecurity outcomes.
Lookout recently launched its generative-AI powered assistant, SAIL, to enhance its cloud-native cybersecurity platform.
AI Index episode 8: Dell announces new offerings with generative AI in its hardware; Thomson Reuters acquires legal AI firm for $650 million; and Lookout launches SAIL to enhance security capabilities.
The Securities Exchange Commission (SEC) now requires disclosure of material cybersecurity incidents and processes for managing cybersecurity threats, reflecting the increasing recognition of technology’s role in business and the need for governance in the digital landscape.
The upcoming SEC rules delve into cybersecurity transparency, incident reporting, and risk management procedures.
GitGuardian’s secrets detection platform adds close to 400 new detectors and the ability to assign severity scores.
The addition of generative AI to Tenable’s exposure management platform makes its functionality more consumable and fuels greater adoption.
Trend Micro is integrating AI into its cybersecurity platform to empower organizations with enhanced capabilities.
There are several security risks associated with generative AI, including AI-powered social engineering attacks and evasion of traditional security defenses.
The potential of generative AI goes far beyond image generation and blog writing—it is a game-changer for staying ahead of evolving cybersecurity threats.
Process mining has several potential cybersecurity applications including incident investigation, anomaly detection, and detecting insider threats.
As cybersecurity teams face escalating demands and the need for faster responses, generative AI tcan help by scanning and summarizing vast amounts of data.
The increasing adoption of cloud services, particularly software-as-a-service (SaaS), has reshaped the role of the chief information security officer (CISO).
In a survey covering hundreds of IT and cybersecurity leaders, Lookout pinpoints areas of complexity and cybersecurity challenges facing financial services firms.
Manual code reviews have limitations in addressing the risks of hard-coded secrets, leading to a critical need for automated analysis in securing the software development process.
Gen AI raises privacy, confidentiality, and security concerns. The C-suite needs a plan for addressing these issues, and edge computing can play a vital role.
Get a preview of “Selling to the New Executive Buying Committee,” an Acceleration Economy Course on vendor selection criteria for multi-cloud and SaaS cybersecurity.