Get a preview of “Selling to the New Executive Buying Committee,” an Acceleration Economy Course on mitigating multi-cloud and SaaS cybersecurity risk while enabling the business.
Search Results: cybersecurity (1380)
Secrets sprawl is a pervasive problem in software security. Acceleration Economy analyst Rob Wood explains how to use automation to prevent exposed secrets in your applications.
Snyk shifts security left with its Deep Code AI Fix, a proprietary AI engine that automates security fixes for developers, enabling risk reduction and addressing vulnerabilities in cybersecurity.
GitGuardian and Snyk join forces to strengthen cloud-native security, enhance their developer-centric approach, and drive early risk mitigation in software development.
Get a preview of “Selling to the New Executive Buying Committee,” an Acceleration Economy Course on top business and tech drivers for multi-cloud and SaaS cybersecurity.
Deepfakes challenge the traditional cybersecurity paradigms. Rob Wood explains how in this Generative AI Digital Summit moment.
Bill Doerrfeld explains how AI is improving endpoint threat detection and accelerating response times.
From a security perspective, AI can be used against itself within the realm of behavioral analytics and malware detection.
The updated Endor Labs platform lets cybersecurity users assess open-source software using natural language search.
Machine learning is nothing new in cybersecurity, but in recent years, it’s gotten significantly better, says Rob Wood.
Rob Wood explains why cybersecurity ML models need clean and ample data, proper input ranges, and robust data platforms, such as the security data lake.
Your competitors are already doing it, so you do not want to put your head in the sand, says Rob Wood.
The integration of machine learning and AI capabilities in cybersecurity offer opportunities for improved specificity, consistency, and scalability.
Security leaders should have conversations with key personnel in HR, finance, and sales/marketing to ensure alignment between security and business goals.
These two complementary cybersecurity practices, when combined, enable organizations to quickly and effectively identify and mitigate potential cyber threats.
Leveraging threat intelligence for operational needs can make organizations more effective and adaptable in modern cybersecurity operations.
The new resource provides intelligence on malicious actors and attack vectors, especially those used in recent software supply chain attacks.
A communications point person is essential after a breach; they keep everyone in the loop, enabling cybersecurity folks to focus on cybersecurity.
Working with multiple partners delivers the best outcomes for enterprises looking to integrate critical elements of modern business infrastructure.
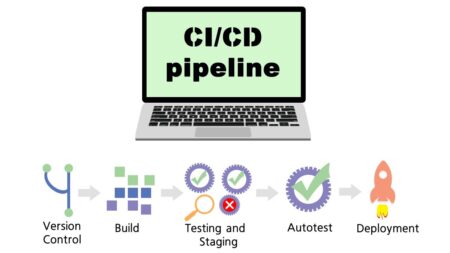
Bill Doerrfeld analyzes the state of modern CI/CD security, reviews the most common risks, and offers some safeguarding suggestions.