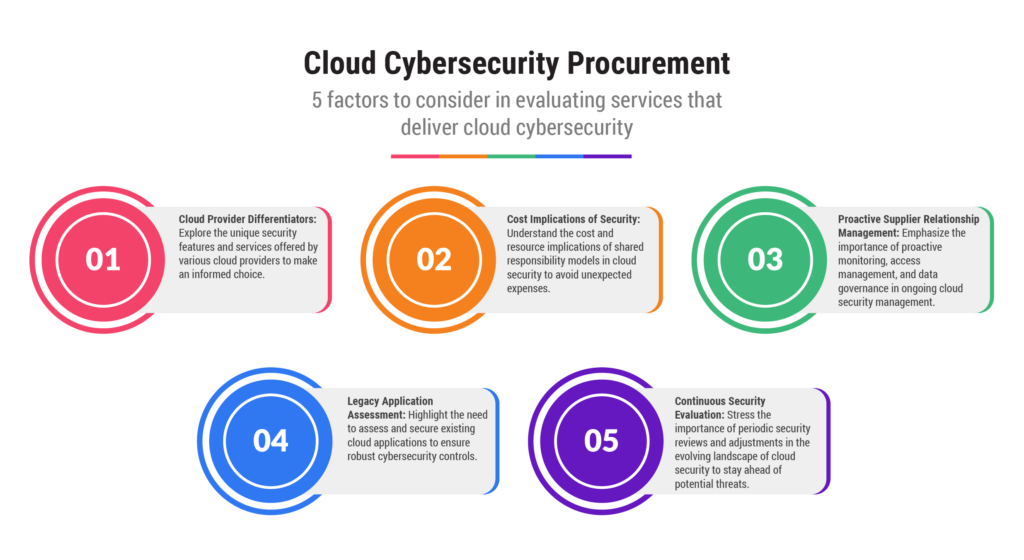
When faced with choosing a supplier among many options, procurement defaults to the request for proposal (RFP). As such, I believe that one of the great values that procurement brings to the buying process is crafting RFP questions. Why? Because when done correctly and collaboratively, the exercise of developing questions forces the business to articulate what it really needs. And given that 79% of all organizations identify security as a top cloud challenge, according to the Flexera 2023 State of the Cloud Report, cybersecurity must be checked when making cloud provider purchasing decisions.
But it’s not always that simple. What if you asked potential cloud service providers (CSPs) about cybersecurity and received responses that look very similar? How would a chief procurement officer (CPO) help the business distinguish among CSPs? This analysis lays out a few approaches.
Ask the Suppliers for Differentiating Data
Ask the suppliers participating in the RFP to differentiate between themselves and their competitors using data, not marketing material. They may describe a point of difference that hasn’t been caught in the RFP.
It’s easy for a business to assume that CSPs like AWS, Microsoft Azure, and Google Cloud are responsible for all aspects of cloud security. After all, they spend significant sums on security, much more than any of the clients on their platforms do for themselves. But according to A Cloud Guru, they each employ a different shared responsibility model. For example, AWS is responsible for the security of its cloud and the physical network and data centers that support it, while the customer is responsible for what they put in the cloud in the form of their data and applications. Others like Azure use a matrix where responsibilities change based on the service model used.
This is an important item to lock down, particularly because there will be costs and headcount involved and a potential cloud client needs to accommodate for that expense. Otherwise, the new environment will be more expensive than planned right off the bat.
Put Robust Supplier Relationship Management in Place
If all the major players offer cybersecurity protection models that are acceptable to a potential client, a CPO can look at what happens after implementation that can be incorporated into a robust Supplier Relationship Management (SRM) program.
Once the transition has occurred, being proactive in dealing with potential security breaches can head off the need to be reactive afterward. Every CSP provides ongoing monitoring services (or works with third parties that do); the key is making sure that the services are being employed as agreed. The following items must consistently be on the agendas for quarterly business reviews:
- Robust access management, because unauthorized access to data is considered one of the biggest risks to cloud security
- Monitoring for unusual activity and adjusting access privileges where needed
- Monitoring user lists
- Scanning and identification of network vulnerabilities
- Data governance
- Inventory management: With new applications going up in the cloud instead of in an on-premise environment, it is easy to lose track of everything that is actually running. Something that’s out-of-sight may slip through the cracks and become easy prey for hackers, so it’s important to sunset applications that are no longer used.
Remember the Applications That Already Reside in the Cloud
During the pandemic, some companies may have sacrificed security for speed, in attempting to get as much up in the cloud as possible to facilitate remote working for their employees. Time to go back, inventory, and assess these legacy systems; do they have the right cybersecurity controls in place? And if a new cloud provider has just been chosen, don’t forget to make sure that existing applications belong in the migration plan so they aren’t forgotten.
Final Thoughts
Security is not to be taken lightly in this era of more sophisticated hackers and larger and more complicated attack surfaces. At first glance, cybersecurity models among cloud providers may seem like near carbon copies of each other, but a bit of digging can yield some real differences that should influence the ultimate choice of CSPs and help a company wind up with the right security framework.
This article has been updated since it was originally published on May 9, 2023.