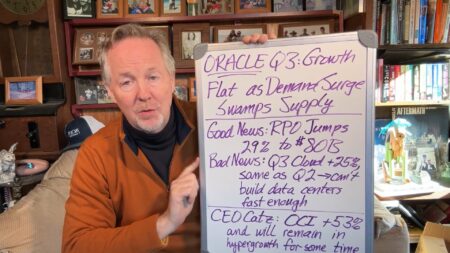
Oracle’s Q3 results reveal both challenges in meeting cloud infrastructure demand and ongoing success in securing large deals.
apps
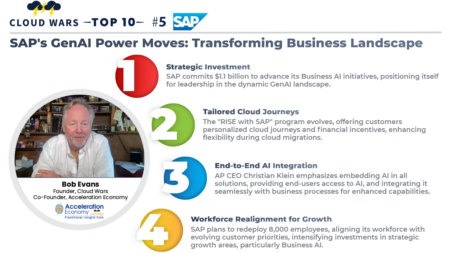
SAP CEO Christian Klein is making a substantial commitment to Business AI, investing $1.1 billion and shifting 8,000 positions amid the GenAI Revolution.
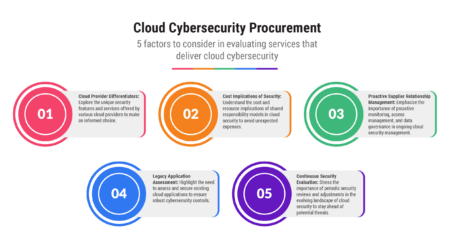
At first glance, cybersecurity models among cloud providers may seem like near carbon copies of each other, but a bit of digging can yield some real differences.
Databricks announces Lakehouse Apps, enabling developers to build and distribute native applications on its Marketplace, providing easy integrations, extended services, and flexibility for developers.
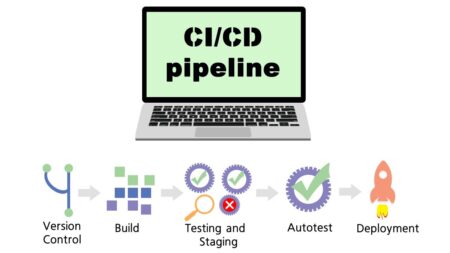
Manual code reviews have limitations in addressing the risks of hard-coded secrets, leading to a critical need for automated analysis in securing the software development process.
Robust encryption, access controls, and user education help CISOs mitigate the risks of theft, insider threats, and cyber attacks against their organizations.
There are unique endpoint security challenges associated with cloud-based systems. Here are some strategies to address them.
Tony Uphoff discusses presentations and conversations from the conference around new ServiceNow platform roadmaps, venture strategies, and recent senior leadership hires.
Don’t just buy tools to improve the effectiveness of data analytics teams; buy into your employees’ future leveraging these tools.
Bill Doerrfeld analyzes the state of modern CI/CD security, reviews the most common risks, and offers some safeguarding suggestions.
JBS manager Steph Robinson shares details on her company’s use of Qlik as a self-service business tool, among other applications.
Qlik software is compared to the data analytics tools Tableau and Power BI.
CEO Ardjan Baan explains how Vanenburg provides its Rappit solution as a foundation for complex customizations.
Resilient organizational culture is the key to success in a world of shifting market dynamics, technological disruptions, and global uncertainties, says Tony Uphoff.
Kieron Allen details how Creatio’s newest no-code training fuels innovation and application development.
In a statement, Lookout exec explains the data collection practices of TikTok and other mobile apps, cites need for awareness of mobile apps’ risk.
As artificial intelligence and language models continue to advance, multilingual language models are vital to the preservation of humanity within technology.
MITRE’s new System of Trust risk model manager and a community engagement group introduces another great resource for software supply chain security and risk management.
One Medical Chief Strategy Officer Jenni Vargas explains how the healthcare platform’s distinct business model works, and why patients are flocking to it.
SAP is now offering another powerful go-to-market engine aimed at what customers want most – ease in deploying and optimizing enterprise apps in the cloud.