In ep. 23, Kieron Allen discusses a strategic concept that considers guidelines and limitations as opportunities for innovation rather than hurdles to overcome.
Cybersecurity
Pushing its sweeping co-creation model with global banks to new levels, IBM will help these financial institutions become more secure, compliant, and resilient but also boost performance.
Too often people only think about cybersecurity after a negative event, but it’s important to be risk-ready all the time, as Frank explains.
In ep. 33 of the Cybersecurity Minute, Frank Domizio explains how organizations have “tabletop training” for incident response in the event of a power outage or ransomware attack.
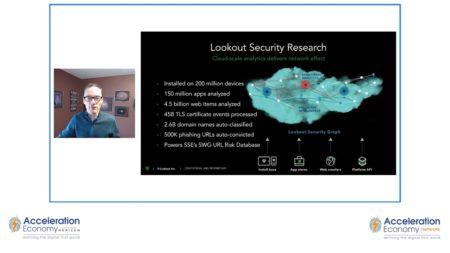
Lookout Principal Technical Marketing Manager Daniel Feller explains how behavior analytics is a foundational element of the Lookout Cloud Security Platform, which focuses on internet security, private apps, and SaaS apps.
In this Cloud Wars Horizon Demo Day moment, Chris Hughes discusses how Chainguard, Grip, and Endor Labs are addressing security issues in new ways.
In this Cloud Wars Horizon Demo Day moment, John Siefert is joined by Aaron Back and Chris Hughes to discuss how businesses must prepare for inevitable data breaches.
Cloud backups are one of the first use cases that the cloud was famed for, and they’re essential for restoring systems after a breach, as Kieron explains in episode 18.
In ep. 53, Tony explains why the cloud, hyperautomation, data modernization, and cybersecurity are the enabling technologies companies will need to transform and modernize in 2023.
Bill reviews ThreatQuotient’s “2022 State of Cybersecurity Automation” report, which finds that the majority of organizations experience pain problems implementing these initiatives.
Bill reconnects with Sonatype Co-founder Brian Fox to find out why it’s taken so long for organizations to respond to the Log4j vulnerability, which was first discovered a year ago.
Bill summarizes the main points from Endor’s 2022 State of Dependency Management study to better understand how cybersecurity professionals should respond to OSS vulnerabilities.
Analyst Robert Wood explains a strategy for resolving data breaches that entails getting inside your adversary’s head.
While the realization of a cybersecurity incident of course brings primary impacts, it doesn’t stop there. In this analysis, Chris explains how and why preparation helps.
In ep. 10, Kieron explains why cybersecurity professionals must prioritize training on cybersecurity issues and prevention.
After a breach, you’ll want to stop data loss as soon as possible, but it comes with risks and other drawbacks. Frank shares tips to arm you with the knowledge, options, and flexibility to advise your business on the right approach.
Burned out security and software teams are hard to retain and increase the odds of a breach. Bill speaks with Object First’s David Bennett, about how he tackles the issue as an object storage solution startup CEO.
After a breach, you’ll need help from an incident response team, either in-house or third party. Frank explains how and what to look for.
In Ep. 6 of the Acceleration Economy Minute, Kieron Allen explains why legal representation is needed for those who wish to succeed in the acceleration economy.
CISO Robert Wood details three techniques to analyze security breaches so that organizations can prevent them in the future.