For CISOs and security leaders, grappling with the global ramifications of the EU AI Act becomes paramount, necessitating a proactive stance.
Search Results: CISO (310)
A look at new guidelines for secure AI system development released by the Cybersecurity Infrastructure and Security Agency and the National Cybersecurity Center in the UK, emphasizing a holistic approach throughout the software development lifecycle.
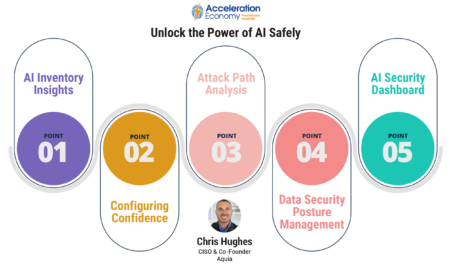
Wiz’s AI Security Posture Management (AI-SPM) addresses security and privacy concerns wrought by AI with comprehensive oversight, inventory management, and misconfiguration checks.
In this guidebook, practitioner analysts and CISOs define how to craft a secure foundation for businesses to thrive in today’s ever-changing digital economy.
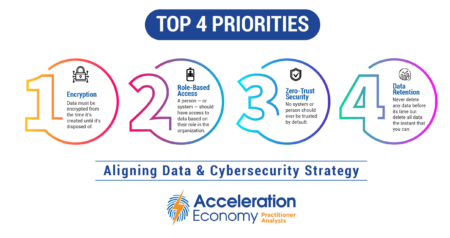
The chief data officer (CDO) and chief information security officer (CISO) should agree on encryption, role-based access, zero trust security, and data retention for effective business decisions and risk mitigation.
This guidebook offers insights into
the challenges of hybrid work in the cloud era, the strengths and weaknesses of traditional
cybersecurity mechanisms aimed at addressing those challenges, and why organizations need a CASB with DLP to control access and protect data at a granular level.
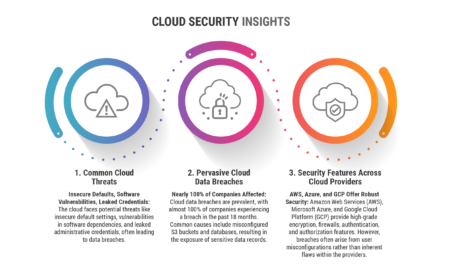
The big three cloud service providers AWS, Azure and Google Cloud share but also differ on features and vulnerabilities.
Ajay Sabhlok emphasizes the critical role of technology and collaboration in data management.
Discover how the NVIDIA-VMware partnership empowers manufacturing with cutting-edge AI technology while addressing security and privacy concerns.
Oracle’s cloud infrastructure business is poised to outgrow its cloud applications business by the end of 2024. Artificial intelligence (AI) companies are embracing its platform.
The Securities Exchange Commission (SEC) now requires disclosure of material cybersecurity incidents and processes for managing cybersecurity threats, reflecting the increasing recognition of technology’s role in business and the need for governance in the digital landscape.
Technology partnerships are significant when it comes to harnessing AI capabilities, presenting both potential risks and opportunities, especially for smaller partners.
Discover the top 10 Low-Code/No-Code vulnerabilities and how to secure rapid development environments.
The Wiz cloud security platform gives comprehensive control over customers’ cloud infrastructure and applications, while providing a visual ‘Graph’ of the environment.
New Lookout service solves an important problem for companies with employees in mainland China, enabling secure, high performance access to data and applications.
Trend Micro is integrating AI into its cybersecurity platform to empower organizations with enhanced capabilities.
There are several security risks associated with generative AI, including AI-powered social engineering attacks and evasion of traditional security defenses.
In a new analysis of the SaaS market, cybersecurity software provider Grip Security identifies nearly 75,000 apps and the resulting attack surface risks.
As cybersecurity teams face escalating demands and the need for faster responses, generative AI tcan help by scanning and summarizing vast amounts of data.
The increasing adoption of cloud services, particularly software-as-a-service (SaaS), has reshaped the role of the chief information security officer (CISO).