Wrapping up this week in style with Aaron Back and John Siefert on Dynamic Communities The Wrap. This episode is…
Security is a foundation of any application and optimal network environment. What role does biometrics play in a passwordless future?
In this episode, “5 Ways Bridget Courneya is Awesome”, Industry Cloud Battleground, Security, Microsoft’s growth, Salesforce app platform, & more
Ethical hacker and best-selling author Ted Harrington joins Aaron Back to discuss security as an enabler, its impact on AI and IoT, and the importance of a security foundation
Aaron Back chats with Greg Ness, CMO, and Shannon Smith, COO of DigitSec about the importance of security at all levels and roles within a company
Understanding the role of a Chief Information Security Office (CISO) is crucial: Key duties include disaster recovery plans and cybersecurity best practices.
By ensuring the security of sensitive information while staying up-to-date with dynamic security needs, you can protect your cyber environment.
Many people try to explain the difference among all roles of the data professional – In this piece, Pablo Moreno adds his own spin on the conversation
Check out this blog to discuss the key steps to avoiding data misuse and internal fraud with Microsoft D365.
Data privacy and protection laws are expanding to more areas of the world. This puts added pressure on organizations to be prepared with their processes.
The CISO is becoming more prominent due to the importance of cybersecurity. Learn critical duties a CISO should embrace to counteract cybersecurity threats.
Security concerns tend to come and go depending on the news of the latest cyber-attacks. But could this turn into a good thing for you and the industry?
This article from HelpNetSecurity (careful of some ads) highlights a recent study from Trend Micro that indicated there are still hurdles in the way of integrating security into business processes. This really shines a light on business not taking security seriously and feeling the impacts from it.
Credit card processing is vital to so many businesses, yet wrought with tedious details, requirements, and contradictory information that drains the souls of CFOs and Controllers worldwide. We’ll examine the myths and facts of this seemingly complex world to help you identify key opportunities for greater efficiencies and lower processing fees.
In this CIO Drive article, Samantha Schwartz outlines the key areas to focus on when presenting security issues to the C-Suite. While presenting this information to the C-Suite is important, many times this presentation lacks information on the impact on the bottom line. This doesn’t translate well when threat levels need to be acted upon in different ways.
Read what Andy Wu of the Harvard Business school thinks about Hackathons – not only do devs – and others – learn new technologies, tech companies have the opportunity to show off their platforms.
With many companies leveraging cloud services today, many take cloud security for granted. Ransomeware, data hacking, and more are becoming more sophisticated, so it’s important to have good DLP policies in place.
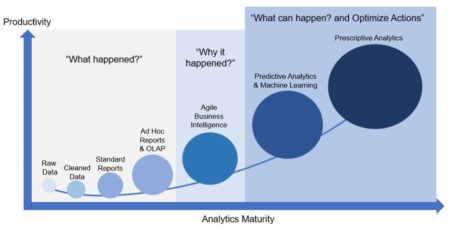
In this insightful article , Eide Bailly explains how to find value in your data and the importance of bringing meaning through a narrative, context and visualization.
Learn the best practices and tips for password safety by Security Intelligence and see why eight characters doesn’t cut it anymore.
Not every organization is facing digital transformation from the same starting line; it is important to evaluate internally and strategize the next steps.