Software composition analysis tools are valuable assets to secure systems and protect organizations, says Frank Domizio, but they will also directly benefit software developers.
Search Results: software (2263)
Analyst Tom Smith sheds light on SaaS software startup Gong, a pioneer in the application of AI to the selling process, which could translate to increased revenue.
When a large oil and gas company in southeast Europe set out to migrate on-premises data and applications to public cloud infrastructure, they turned to Lookout to help address the myriad of security challenges that emerged.
In ep. 17, Kieron reviews Bill Doerrfeld’s recent report on workplace burnout among software development and cybersecurity teams.
How MongoDB, UiPath, Couchbase, and Cloudflare beat expectations and raised their outlook amid challenging macroeconomic conditions.
Bill Doerrfeld summarizes the key points from Sonatype’s “The State of the Software Supply Chain” report to help IT technology divisions better understand how to address open-source security today.
El uso de soluciones de código abierto crece más de un 33% interanual, también las amenazas y ciberataques inherentes a estas soluciones.
Non-tech industry lines are becoming more blurred. Bob Evans describes how Google Cloud and the Renault Group are joining forces to create a software-defined vehicle.
In episode 31, Chris Hughes explains the NSA’s recent release of software supply chain security guidance for developers.
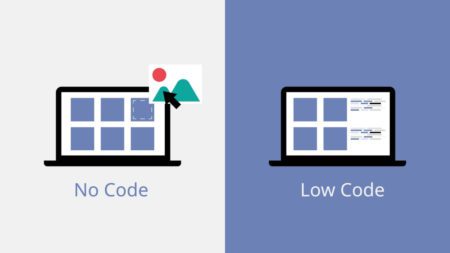
CIO Kenny Mullican covers a set of tools that are a very cost-effective way to keep a project in-house —without the need to hire a large developer team and produce quick results.
In Cybersecurity Minute, Ep. 31, Chris Hughes says it’s clear that the Senate’s Securing Open Source Software Act emphasizes how critical open-source software is to national security and society.
As Chris Hughes explains, the recent U.S. government response to increased software supply chain attacks will force the cybersecurity industry to innovate.
Celonis occupies a unique position in the software industry: It doesn’t manage core business functions like an ERP system, yet it delivers an outsized financial impact for its customers.
From VR headsets and souped-up PCs to 3D meeting spaces and crypto wallets, here are the hardware and software requirements you’ll need to enjoy the Metaverse.
In this Cybersecurity Minute, Ep. 23, Chris Hughes details the CIS software supply chain security benchmark, which was developed alongside Aqua Security.
The discovery includes malicious code with more than 17,000 harmful downloads, says Chris Hughes in Cybersecurity Minute, Episode 21.
This is the second in a series of three ASUG Guest Perspectives contributed by Bob Evans, Acceleration Economy co-founder, Cloud Wars founder, and digital business expert.
Celonis Chief Customer Officer Malhar Kamdar says the enterprise software company’s clients are moving projects ahead with increased urgency.
Customers have high urgency to deploy software that delivers measurable value – especially when it’s an add-on to core systems, Celonis’ chief customer officer says.
In this Cybersecurity Minute, Ep. 19, Chris analyzes the CNCF releasing its Secure Software Factory guidance and what it means for software security.